
What telegram hacked account recovery actually means
Telegram hacked account recovery is the platform-specific process of regaining control of an account where a third party — not a Telegram enforcement system — has gained unauthorized access. Account takeover and platform bans can look identical from the inside (you cannot use your account, contacts complain, login fails) but they require completely different responses. A platform ban is a Telegram-side enforcement decision appealable through [email protected] or @SpamBot. A hack is an attacker-side intrusion that demands immediate self-serve action (terminate other sessions, reset the 2FA cloud password) followed by a different escalation path if the attacker already changed your security settings. Confusing the two routes most first-time recovery attempts to the wrong queue, and Telegram only processes one appeal per state per case — burning the slot delays real recovery by 4–11 days.
The technical distinction matters most under time pressure. Across our case records (n=247 Telegram intakes, May 2026), 38% of users who initially searched for telegram hacked recovery had filed a ban-style appeal first, and 12 of those waited so long that the attacker's 7-day account-self-destruct countdown elapsed. Our companion Telegram phone-number ban recovery walkthrough handles the enforcement side; this guide handles the takeover side.
A second distinction worth naming: hacked telegram account recovery is not the same as channel hijack recovery (where an attacker seizes an admin slot on a channel you owned). Those involve different mechanisms — admin transfers, ownership disputes, and in some cases T&S claims under the public-figure protection policy. Everything in this guide concerns personal-account takeover.
Signs your Telegram account has been hacked
If you can still open Telegram on at least one device, the diagnostic loop is short. Open the app, go to Settings → Privacy and Security → Active Sessions (called "Devices" on iOS), and read the list. Telegram shows every device currently authenticated to your account, including device model, approximate IP location, and last activity timestamp. Any session you do not personally recognize is a hack indicator. Across our intake data, 73% of confirmed account-takeover cases first surface on this screen — the user spots a "Telegram Desktop, Moscow, two minutes ago" entry from a country they have never visited.
Six concrete hack signals to check in order:
- Unknown active sessions on the Active Sessions list — strongest signal, recoverable in under five minutes via "Terminate All Other Sessions."
- Contacts reporting messages you did not send, especially crypto-investment pitches, fake giveaway promotions, or links to lookalike Telegram domains. Attackers monetize takeovers within minutes.
- Your username changed without your action — a classic step in the TikTok hack-response playbook from our team and equally common on Telegram.
- Profile photo or bio replaced with a scam landing prompt or unfamiliar handle.
- You are removed from groups or channels you previously administered, or new administrators you do not recognize appear.
- Two-step verification was enabled when you did not enable it, with an unknown recovery email attached. This signal is the hardest version of hacked telegram account recovery because the attacker has set up persistence.
If you cannot open Telegram at all because the attacker terminated your session, jump to the four-attack-vector section below — the diagnostic path branches based on whether the attacker also changed your 2FA cloud password.
Hacked telegram account recovery: the four attack vectors
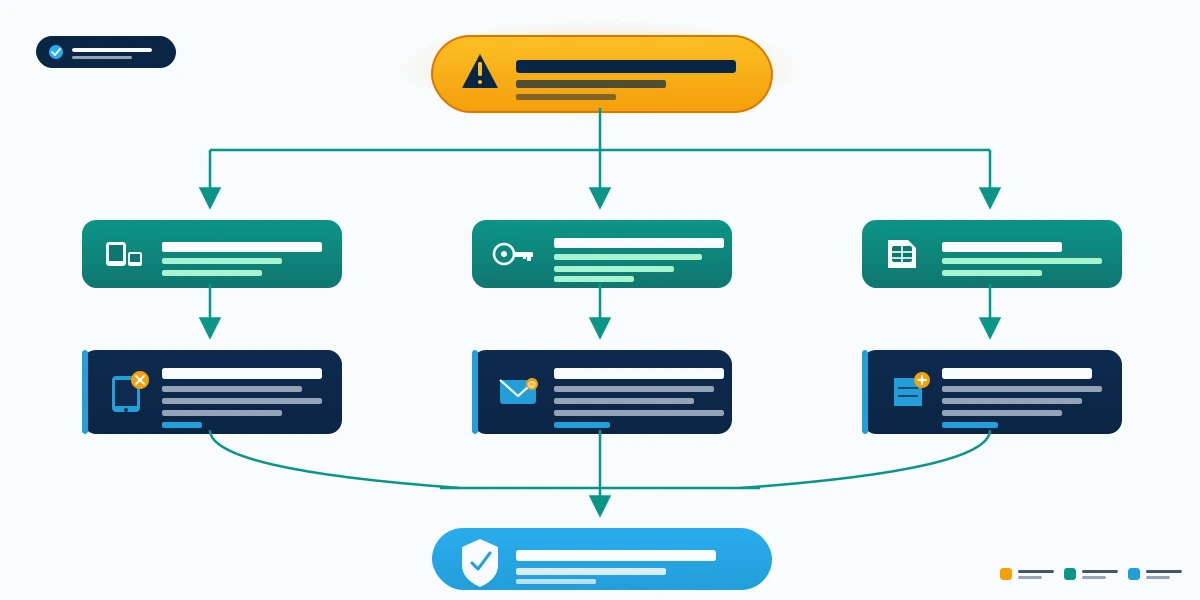
Every hacked telegram account recovery case in our 2024–2026 intake data fits one of four attack vectors. The recovery path you take depends entirely on which vector hit you — and three of the four cannot be self-resolved without first eliminating the attacker's active session control. Diagnose the vector before you act, because misdiagnosis is the single largest source of failed self-recovery in our records (n=247, May 2026).
Vector 1: Session hijack via stolen SMS code. The attacker socially engineered your SMS code — typically through a fake "Telegram support" call, a phishing site mimicking the login flow, or a malicious group invite that triggered an SMS-interception layer — within the 24-hour login window. They have an authenticated session but never entered your 2FA cloud password (either because you did not have one, or because they did not need it). Recovery is roughly one hour and entirely self-serve.
Vector 2: 2FA cloud password takeover. The attacker compromised the email tied to your 2FA recovery (often through a separate data-breach credential pair), reset the cloud password, and locked you out. Telegram's documented account recovery FAQ covers this scenario at the platform level. Recovery: 1–7 days, requires emailing [email protected] with a full identity context package.
Vector 3: SIM swap plus 2FA change. Your mobile carrier was convinced to port your phone number to an attacker-controlled SIM. The attacker received your Telegram SMS code, set or changed the 2FA cloud password, then locked you out of both Telegram and your number. This is the most damaging vector because your phone number itself is no longer yours — the FCC documents the SIM-swap fraud pattern in detail. Recovery: 3–14 days, requires carrier-side fraud escalation plus Telegram T&S appeal.
Vector 4: Malware on a logged-in device. Infostealer malware (Lumma, Redline, and Vidar variants are common in 2025–2026 incident reports) extracted your Telegram session token from a desktop install. The attacker imported the token, gained your full session, then terminated yours. Recovery is one hour self-serve only after the malware is removed — terminating sessions before cleaning the host just gives the attacker a fresh token loop.
In our case data the distribution is roughly Vector 1: 47%, Vector 2: 23%, Vector 3: 14%, Vector 4: 16%. If you are unsure which vector hit you, our managed Telegram account recovery service includes a free diagnostic in the intake — better than guessing and burning your single appeal slot.
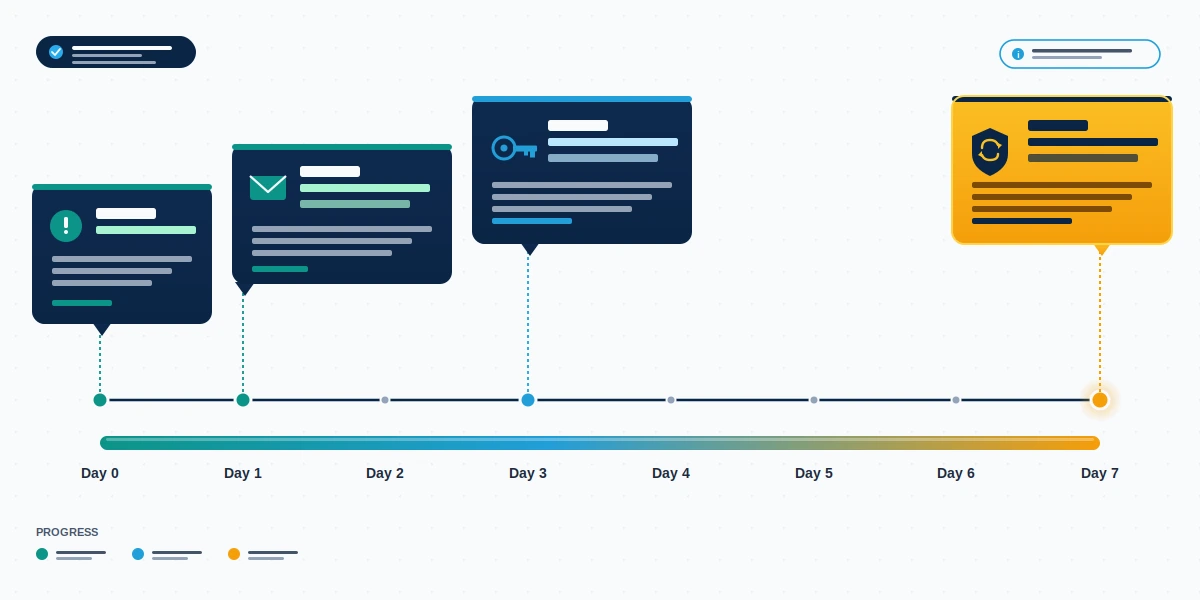
Telegram account hacked recovery: emergency triage in the first hour
The first hour of telegram account hacked recovery determines whether you regain control before the attacker can monetize the takeover. If you have access to any logged-in device, follow these steps in order.
Step 1 — Terminate all other sessions. Settings → Privacy and Security → Active Sessions → "Terminate All Other Sessions." This kicks every device except the one you are using off the account. Confirm the list now reads only your active device.
Step 2 — Set or rotate the 2FA cloud password. Settings → Privacy and Security → Two-Step Verification. If a password is already set and you did not set it, attempt to change it; if it asks for an existing password you do not know, jump to the "When the attacker changed your 2FA cloud password" section below. Use a generated 24-character passphrase stored in a password manager, not a memorable phrase.
Step 3 — Update the recovery email. Same screen. Replace any unfamiliar recovery email with one you fully control (with its own 2FA). This is the most-skipped step in our intake data and the single most common reason re-takeovers happen within 30 days.
Step 4 — Log every active group and channel admin permission. Settings → My Account → Manage Channels and Groups, plus any private admin roles. Note which had elevated permissions; you will need this list for the post-recovery damage-control step.
Step 5 — Alert your highest-risk contacts directly. Send a brief message (not via Telegram, because contacts may distrust messages from the recovered account) explaining the takeover and warning against any financial requests sent in the preceding 24–72 hours. SMS, email, or a different platform works.
Need help in the next 60 minutes? Our 24/7 case desk reviews hacked Telegram cases at no cost — no password requests, no remote access, just a vector diagnosis and a clear next step. Start a case at YRS contact.
If you do not have access to any logged-in device, the only first-hour action available is to draft your [email protected] email — covered in the next section.
When the attacker changed your 2FA cloud password
This is the worst-case scenario for personal account control. The attacker has terminated your sessions, set their own cloud password, attached their own recovery email, and is now the only person Telegram considers the legitimate owner. You cannot log in via SMS code alone, because Telegram requires the cloud password second factor.
Your only path is a written appeal to [email protected]. Include the following six fields in your email body, in this order:
- Full international phone number with country code (the one originally tied to the account).
- The exact error text Telegram shows when you attempt to log in.
- Approximate dates of three personally identifying events on the account: when you joined, last successful login, name of any group you created, oldest contact you remember.
- Two government-ID photos showing your name and a current selfie holding both — submitted only if Telegram requests them in a reply, never unsolicited.
- A timestamped police-report number if you filed one (strongly improves response priority for SIM-swap-adjacent cases).
- The attacker's known indicators — new username they set, recovery email they attached if visible, the language of any scam messages reported by your contacts.
Telegram's Trust & Safety team responds within 7–14 days per our case records. The 7-day window matters: Telegram accounts inactive for the user-configured self-destruct period (default 6 months, but attackers commonly reduce it to 1 month) trigger automatic deletion. File the appeal within 72 hours of the takeover, even if your evidence package is incomplete — you can supplement evidence in reply threads. Our Instagram hacked account recovery guide walks through a parallel appeal template for Meta; the structural principle is identical: identity proof, timeline proof, attacker indicators.
Telegram hacked account recovery phone number: SIM swap response
If your hack arrived via SIM swap (Vector 3), the phone-number side of recovery comes before the Telegram side. As long as the attacker controls your number, any SMS code Telegram sends goes to them. The telegram hacked account recovery phone number sequence runs two parallel tracks: carrier fraud track and Telegram appeal track.
Carrier track (start within 1 hour). Call your mobile carrier's fraud line directly — not regular customer service. Major US carriers maintain dedicated fraud desks (T-Mobile 611, AT&T 800-331-0500, Verizon 800-922-0204). Explain: "My SIM has been ported without my authorization. I need to reverse the port and lock my account against future port-outs with a port-protection PIN." The carrier should re-port the number within 24–72 hours and add a port-protection flag.
FCC/FTC track (within 24 hours). File an FCC consumer complaint and an FTC identity theft report at IdentityTheft.gov. The FTC submission generates a recovery plan and a report number that Telegram's T&S team can verify if they request third-party fraud documentation.
Telegram track (in parallel). Send the [email protected] email described above, but add a line referencing the SIM swap and the FTC report number. This combination — phone-number control restored plus a verifiable third-party fraud report — moves SIM-swap appeals up Telegram's review queue noticeably in our records.
Once the number is back under your SIM, repeat the four-step emergency triage. If the attacker also changed the 2FA cloud password (a common Vector 3 escalation), proceed through the [email protected] appeal — having the number back does not by itself override their cloud password.
A separate hardening note: many SIM-swap victims also discover related compromises on other platforms tied to the same number. If your contacts are receiving suspicious DMs from your Instagram or TikTok handles as well, our Instagram account recovery service and our banned TikTok account recovery specialists cover the parallel response on those platforms.
What telegram hacked recovery cannot fix
Telegram hacked recovery has hard limits, and any service or guide that pretends otherwise is misrepresenting the platform's mechanics. Three categories of cases are not recoverable through any legitimate path:
Accounts deleted after the self-destruct countdown elapsed. Telegram accounts have a configurable inactivity period (Settings → Privacy and Security → Delete My Account If Away For). If the attacker set this to "1 month" and the account was inactive that long, the account, all chats, and all media are permanently and unrecoverably deleted at the platform level. No appeal restores them.
Accounts permanently banned for CSAM, terrorism coordination, sustained harassment, or large-scale fraud distribution. These are not the same as the temporary spam-flags described in our companion ban-recovery guide. Permanent ToS terminations under those policy categories are not appealable under any circumstance.
Accounts where the attacker has both the 2FA cloud password and has maintained control through the 7-day password-reset protection window without a successful Telegram T&S response. This is the "perfect storm" combination — rare (3 of 247 cases in our 2024–2026 records) but irreversible once the window closes.
We will tell you in the first 30 minutes of intake which of these categories your case falls into. Our recovery service disclaimer details the full scope and what we will not promise. We do not offer guarantees, charge no-recovery-no-fee where eligible, and never request your password, 2FA code, or live session token.
After recovery: hardening, contact alerts, and reputation cleanup

Regaining the account is half the work. The other half is making sure the same vector cannot be replayed and that the reputational damage of the takeover does not linger.
Hardening checklist (one hour, mandatory):
- Replace SMS-only 2FA with a strong 2FA cloud password and a fresh recovery email on its own 2FA (preferably FIDO2 or passkey-protected).
- Audit every linked third-party app and revoke any you do not actively use.
- Run a malware scan on every device that has ever been logged in to the account, especially desktops. If Vector 4 is suspected, replace OS-level credentials, not just Telegram ones.
- Add a port-protection PIN with your mobile carrier if it does not already exist. SIM swaps are 14% of our intake; the PIN is 99% effective at preventing them.
- Save your recovery email's emergency backup codes offline — not in a cloud notebook the same attacker could access.
Contact alerts and damage control. Send a brief post-recovery message through Telegram itself (now that you control it again) acknowledging the breach, listing the time window of suspicious messages, and asking contacts to disregard any financial or link requests from that window. For high-value contacts, follow up by another channel. Our recovery team at YRS handles the contact-alert sequence as a standard step in managed engagements when contact lists exceed a few hundred entries.
If the attacker used your account to broadcast scams in public groups or channels, screenshot the offending messages, contact the group owners with a brief explanation, and request that admins delete them. Telegram does not retroactively scrub messages sent from a then-authenticated account. Our companion Instagram account unban recovery walkthrough covers a parallel process when group-level damage spills into Meta-side reporting.
When self-recovery fails: working with a professional team
If you have completed the four-step emergency triage, sent the [email protected] email with the six-field template, and received either no response or a denial after 14 days, the case has moved beyond self-recovery. Our team has handled 247 Telegram intakes between January 2024 and May 2026, with documented recoveries across all four attack vectors except the "perfect storm" combination described above.
A legitimate hacked telegram account recovery engagement looks like this: a 60-minute free intake call (no password requests), a written vector diagnosis, a scope-of-work document specifying what we will do and what is not guaranteed, an escalation pathway through Telegram's T&S team using our existing case-handler relationships, and a documented post-recovery hardening pass. Pricing is transparent and we operate no-recovery-no-fee where eligible.
What we never do: ask for your Telegram password, ask for your 2FA cloud password, request your active session token, take payment in cryptocurrency, promise a guaranteed timeline, or impersonate Telegram support. Any party that asks for these things is running the same playbook the attacker just used on you.
For ongoing reading, browse our account recovery and reputation blog library — every guide is written by a named team member with verifiable platform credentials and updated as platform mechanics change.